Filter by
Cyber security awareness for CEOs and management
Cyber Security for CEOs and Managment is a concise overview of the security threats posed to organizations and networks by the ubiquity of USB Flash Drives used as storage devices. The book will provide an overview of the cyber threat to you, your business, your livelihood, and discuss what you need to do, especially as CEOs and Management, to lower risk, reduce or eliminate liability, and pro…
- Edition
- -
- ISBN/ISSN
- 9780128047545
- Collation
- xi, 42 hm.: ilus.; 23 cm
- Series Title
- -
- Call Number
- 658.4 WIL c
Cyber security awareness for corporate directors and board members
- Edition
- -
- ISBN/ISSN
- 9780128047569
- Collation
- xi, 40 hlm.: ilus.; 23 cm
- Series Title
- -
- Call Number
- 658.40058 WIL c
- Edition
- -
- ISBN/ISSN
- 9780128047569
- Collation
- xi, 40 hlm.: ilus.; 23 cm
- Series Title
- -
- Call Number
- 658.40058 WIL c
Bahan ajar fundamental keamanan informasi
DAFTAR ISI BAB 1 PENGENALAN KEAMANAN INFORMASI A. Tujuan Pembelajaran B. Pendahuluan C. Sejarah Keamanan Informasi D. Definisi Keamanan Informasi E. Konsep C.I.A. F. Beberapa Istilah dalam Keamanan Informasi G. Arsitektur Keamanan Informasi H. Keamanan dalam System Life Cycle I. Evaluasi / Soal Latihan BAB 2 URGENSI KEAMANAN INFORMASI A. Tujuan Pembelajaran B…
- Edition
- -
- ISBN/ISSN
- -
- Collation
- iv, 183 hlm.; ilus.; 30 cm
- Series Title
- -
- Call Number
- 005.8 ARI b
Bahan ajar pemrograman jaringan dengan Python
Daftar isi: BAB 1 KONSEP BAHASA PEMROGRAMAN PYTHON 1.1 Tujuan Pembelajaran 1.2 Pendahuluan 1.3 Python VS Bahasa Pemrograman Lain BAB 2 KONSEP PEMROGRAMAN BERORIENTASI OBJEK PYTHON 2.1 Tujuan Pembelajaran 2.2 Pendahuluan 2.3 Kondisi 2.4 Perulangan 2.5 Control Structure 2.6 Function 2.7 Modules 2.8 Exceptions BAB 3 PEMROGRAMAN SOCKET 3.1 Tujuan Pembelajaran 3.2 Pen…
- Edition
- -
- ISBN/ISSN
- -
- Collation
- v, 197 hlm
- Series Title
- -
- Call Number
- 004.6 DON b
Bahan ajar perimeter keamanan jaringan
DAFTAR ISI BAB 1 Mengenal Keamanan Perimeter Jaringan A. Tujuan Pembelajaran B. Pendahuluan C. Terminologi D. Defense in Depth E. Studi Kasus Defense in Depth BAB 2 Firewall A. Tujuan Pembelajaran B. Pendahuluan C. Definisi Firewall D. Tujuan Firewall E. Teknik yang digunakan Firewall F. Arsitektur Firewall G. Tipe-tipe Firewall H. Praktikum Instalasi…
- Edition
- -
- ISBN/ISSN
- -
- Collation
- vi, 298 hlm.; ilus.; 30 cm
- Series Title
- -
- Call Number
- 005.8 OBR b
Deteksi intrusi menggunakan Python
Daftar isi Bab 1 Deteksi Intrusi Web server Log server Intrusion Detection System (IDS) Metode deteksi Anomali protokol Jenis serangan yang dapat dideteksi IDS Data mining dan kaitannya dengan IDS Bab 2 Data mining Sejarah data mining Pengertian data mining Penerapan data mining Metode pembelajaran dalam data mining Peran dan funsi data mining Bab 3 Ba…
- Edition
- -
- ISBN/ISSN
- 9786237715719
- Collation
- xiv, 156 hlm.; ilus.; 20cm.
- Series Title
- -
- Call Number
- 005.8 KUR d

Hunting cyber criminals: a hacker's guide to online intelligence gathering to…
- Edition
- -
- ISBN/ISSN
- 9781119540922
- Collation
- xxxi, 503 hlm.: ill.; 24 cm
- Series Title
- -
- Call Number
- 005.84 TRO h
- Edition
- -
- ISBN/ISSN
- 9781119540922
- Collation
- xxxi, 503 hlm.: ill.; 24 cm
- Series Title
- -
- Call Number
- 005.84 TRO h
CISSP all-in-one exam guide
null
- Edition
- Seventh Edition
- ISBN/ISSN
- 9780071849616
- Collation
- xxxiv, 1341 hlm.: ilus.; 24 cm + 1 CD
- Series Title
- -
- Call Number
- 005.8 HAR c
Code and other laws of cyberspace
Terdapat bibliografi dan indeks. Table of contents: Ch. 1. Code is law Ch. 2. Four puzzles from cyberspace Ch. 3. Is-ism : is the way it is the way it must be? Ch. 4. Architectures of control Ch. 5. Regulating code Ch. 6. Cyberspaces Ch. 7. What things regulate Ch. 8. The limits in open code Ch. 9. Translation Ch. 10. Intellectual property Ch. 11. Privacy Ch. 12. Free speech Ch.…
- Edition
- Second edition
- ISBN/ISSN
- 9780465039142
- Collation
- xvii, 410 hal.; 24 cm
- Series Title
- --
- Call Number
- 343 LES c2
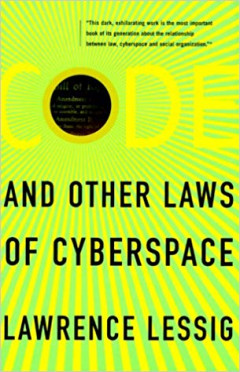
Code and other laws of cyberspace
Terdapat bibliografi dan indeks. Table of contents: Pt.1 Regulability Code is law Four puzzles from cyberspace Is-Ism Architectures of control Regulating code Pt.2 Code and other regulation Cyberspaces What things regulate Thhe limits in open source Pt.3 Applications Translation Intellectual property Privacy Free speech Interlude Sovereignty Pt.4…
- Edition
- First edition
- ISBN/ISSN
- 0465039138
- Collation
- xii, 297 hal 25 cm
- Series Title
- --
- Call Number
- 343 LES c
 Computer Science, Information & General Works
Computer Science, Information & General Works  Philosophy & Psychology
Philosophy & Psychology  Religion
Religion  Social Sciences
Social Sciences  Language
Language  Pure Science
Pure Science  Applied Sciences
Applied Sciences  Art & Recreation
Art & Recreation  Literature
Literature  History & Geography
History & Geography